By Raphael Satter
WASHINGTON, March 11 (Reuters) - A foreign hacker compromised files relating to the FBI’s investigation of the late sex offender Jeffrey Epstein during a break-in at the bureau’s New York Field Office three years ago, according to a source familiar with the matter and recently published Justice Department documents reviewed by Reuters.
The details of who accessed a server at the FBI’s New York Field Office, including the allegation that a foreign hacker was involved, are being reported here for the first time.
In a statement, the FBI said what it described as a "cyber incident" was "an isolated one."
"The FBI restricted access to the malicious actor and rectified the network. The investigation remains ongoing, so we do not have further comments to provide at this time."
Although the source said the intrusion appeared to have been carried out by a cybercriminal rather than a foreign government, the incident underscores the files' potential intelligence value, one academic said. The legally mandated publication of U.S. Justice Department documents has exposed the dead financier's ties to prominent people in politics, finance, academia and business, triggering investigations in numerous countries around the world.
“Who wouldn’t be going after the Epstein files if you’re the Russians or somebody interested in kompromat?” said Jon Lindsay, who researches the role of emerging technology in global security at the Georgia Institute of Technology. “If foreign intelligence agencies are not thinking seriously about the Epstein files as a target, then I would be shocked.”
The breach was reported contemporaneously by CNN and Reuters on February 17; the connection to Epstein materials was made by the French magazine Marianne.
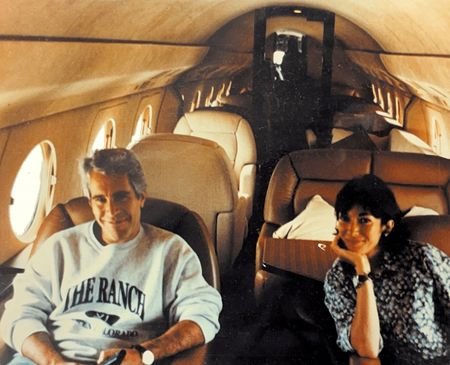
Epstein, a longtime associate of President Donald Trump, pleaded guilty in 2008 to prostitution charges, including soliciting an underage girl. He was found hanged in his jail cell in 2019, in what was ruled a suicide, after being arrested again on federal charges of sex trafficking of minors.
FEBRUARY 2023 BREAK-IN
The hack occurred after a server at the Child Exploitation Forensic Lab in the FBI’s New York Field Office was inadvertently left vulnerable by Special Agent Aaron Spivack, who was trying to navigate the bureau’s complex procedures for handling digital evidence, according to the source and the documents.
A timeline written by Spivack and included in the large cache of Epstein documents released earlier this year said the break-in happened on February 12, 2023. It was discovered the following day when Spivack turned on his computer and discovered a text file warning him that his network had been compromised, according to that document.
Further investigation turned up traces of unusual activity on the server, the document said, adding that the activity "included combing through certain files pertaining to the Epstein investigation.”
The timeline does not say which specific files were accessed, whether the hacker downloaded the data, or who the hacker was. Reuters could not establish what, if any, overlap the affected data had with the Epstein documents published earlier this year or the files that remain under wraps.
Spivack, whose name appears elsewhere in the documents in connection with the Epstein investigation, did not return repeated messages seeking comment. Reuters was unable to reach the man identified in the documents as Spivack’s lawyer, Richard J. Roberson, Jr. Seven FBI agents identified in the documents as being involved in the investigation into the incident did not return messages.
HACKER, FBI CHATTED BY VIDEO
In his statement to FBI investigators examining whether he was responsible for the breach, Spivack said he was being made "a scapegoat for the intrusion" and that conflicting bureau policies and faulty guidance around information technology were to blame. Reuters could not establish the result of the bureau's internal investigation.
The person familiar with the breach said the intrusion was carried out by a foreign hacker who did not appear to realize they had penetrated a law enforcement server. The hacker expressed disgust at the presence of child abuse images on the device and left a message threatening to turn its owner over to the FBI, the person said.
The source said bureau officials defused the situation by convincing the hacker that they actually were the FBI, in part by having the hacker join a video chat where they flashed their law enforcement credentials in front of a web camera.
Reuters could not determine - and the source said they did not know - who the hacker was, what country they were operating from, what they did with the material accessed, or whether any effort was made to identify or punish them for breaking into the FBI’s server.
Many of the Justice Department's documents have been heavily redacted and others have been kept secret altogether despite a law mandating their full release last year. The Trump administration says it is withholding material that could compromise victims’ identities or jeopardize ongoing investigations.
(Reporting by Raphael Satter; editing by David Gaffen)